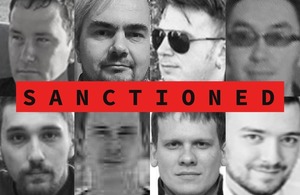
UK sanctions members of Russian cybercrime gang
UK sanctions members of Russian cybercrime gang responsible for attacks on hospitals and critical infrastructure.
- sanctions hit 11 from Russian cyber gang that targeted hospitals and other critical infrastructure
- sanctions will disrupt ransomware attacks and expose attackers behind them
- new measures delivered in coordinated effort with the United States
Members of a Russian cyber criminal gang behind the Trickbot/Conti ransomware attacks, which included the hacking of critical infrastructure and hospitals during the COVID-19 pandemic, face new sanctions today (7 September).
Eleven cyber criminals, whose gang also threatened those who oppose the illegal Russian invasion of Ukraine, have been targeted with asset freezes and travel bans in a coordinated effort by UK and US authorities to counter the threat of ransomware both in the UK and abroad. The US Department of Justice (DOJ) is concurrently unsealing indictments against seven of the individuals designated today.
The National Crime Agency (NCA), who conducted a complex investigation into these individuals, assesses that the group was responsible for extorting at least $180 million from victims globally, and at least £27 million from 149 UK victims. The attackers sought to target UK hospitals, schools, local authorities and businesses.
The individuals being designated in the UK are:
- Andrey Zhuykov was a central actor in the group and a senior administrator. Known by the online monikers ‘Defender’, ‘Dif’ and ‘Adam’
- Maksim Galochkin led a group of testers, with responsibilities for development, supervision and implementation of tests. Known by the online monikers ‘Bentley’, ‘Volhvb’ and ‘Max17’
- Maksim Rudenskiy was a key member of the Trickbot group and was the team lead for coders. Known by the online monikers ‘Buza’, ‘Silver’ and ‘Binman’
- Mikhail Tsarev was a mid-level manager who assisted with the group’s finances and overseeing of HR functions. Known by the online monikers ‘Mango’, ‘Fr*ances’ and ‘Khano’
- Dmitry Putilin was associated with the purchase of Trickbot infrastructure. Known by the online monikers ‘Grad’ and ‘Staff’
- Maksim Khaliullin was an HR manager for the group. He was associated with the purchase of Trickbot infrastructure including procuring Virtual Private Servers (VPS). Known by the online moniker ‘Kagas’
- Sergey Loguntsov was a developer for the group. Known by the online monikers ‘Begemot’, ‘Begemot_Sun’ and ‘Zulas’
- Alexander Mozhaev was part of the admin team responsible for general administration duties. Known by the online monikers ‘Green’ and ‘Rocco’
- Vadym Valiakhmetov worked as a coder and his duties included backdoor and loader projects. Known by the online monikers ‘Weldon’, ‘Mentos’ and ‘Vasm’
- Artem Kurov worked as a coder with development duties in the Trickbot group. Known by the online moniker ‘Naned’
- Mikhail Chernov was part of the internal utilities group. Known by the online monikers ‘Bullet’ and ‘m2686’
This action was taken in coordination with the US, where these key cybercriminals have also been sanctioned, and is a continuation of joint efforts by the UK and US to disrupt and impose costs on high harm cyber criminals. It is assessed that sanctions have hampered the ability of cyber threat actors to monetise their cyber criminal activities.
Foreign Secretary James Cleverly said:
These cyber criminals thrive off anonymity, moving in the shadows of the internet to cause maximum damage and extort money from their victims.
Our sanctions show they cannot act with impunity. We know who they are and what they are doing.
By exposing their identities, we are disrupting their business models and making it harder for them to target our people, our businesses and our institutions.
The individuals, all Russian nationals, operated out of the reach of traditional law enforcement and hid behind online pseudonyms and monikers – many of which are revealed today. Removing their anonymity undermines the integrity of these individuals and their criminal businesses that threaten UK security.
Several of those facing sanctions today held significant roles within the group. Those targeted include high-level managers and administrators, as well as two individuals, Maksim Khaliullin and Mikhail Tsarev, who focused on recruiting and inducting new members.
The group was also one of the first to offer support for Russia’s invasion of Ukraine, maintaining links and receiving tasking from the Russian Intelligence Services.
Deputy Prime Minister and Secretary of State in the Cabinet Office Oliver Dowden said:
By targeting these malicious cyber actors, who have been known to work with some of the most damaging ransomware strains, we are seeking out and exposing those who threaten the UK’s national security. We will always take decisive action with international partners to protect the UK, its people and businesses.
Security Minister Tom Tugendhat said:
These sanctions demonstrate that the UK will crackdown on those trying to hold UK businesses and infrastructure to ransom. We will use our law enforcement agencies to go after the perpetrators and punish their crimes.
We have the skills and resources to find and unmask criminals who attempt to steal from British businesses, schools and hospitals.
We will keep working with our partners, like the US, to defeat these threats.
NCA Director General of Operations Rob Jones said:
These sanctions are a continuation of our campaign against international cyber criminals.
Attacks by this ransomware group have caused significant damage to our businesses and ruined livelihoods, with victims having to deal with the prolonged impact of financial and data losses.
These criminals thought they were untouchable, but our message is clear: we know who you are and, working with our partners, we will not stop in our efforts to bring you to justice.
National Cyber Security Centre (NCSC) Chief Executive Officer Lindy Cameron said:
Alongside this latest round of sanctions, I strongly encourage organisations to proactively obstruct the activities of ransomware operatives by bolstering their online resilience.
Ransomware continues to be a significant threat facing the UK and attacks can have significant and far-reaching impact.
The NCSC has published free and actionable advice for organisations of all sizes on how to put robust defences in place to protect their networks.
Today’s sanctions announcement reinforces the UK’s commitment to cracking down on cyber criminals. They follow on from the first ever joint UK-US sanctions against ransomware actors in February this year. The total number of group members sanctioned is now 18.
View the full UK Sanctions List and more information about UK sanctions relating to Russia.
Background
- if you are the victim of a ransomware attack, you should use the UK government’s Cyber Incident Signposting Site as soon as possible for direction on which agencies to report your incident to
- the Office of Financial Sanctions Implementation has published guidance, which sets out the implications of sanctions in ransomware cases
- making funds available to the individuals such as paying ransoms, including in cryptoassets, is prohibited under these sanctions
- organisations should have or should put in place robust cyber security and incident management systems in place to prevent and manage serious cyber incidents
- the FCDO announced the first wave of sanctions and the launch of the UK-US campaign of coordinated action against ransomware actors on 9 February 2023
- as announced on 29 August 2023, an international operation, led by the FBI and involving the NCA, took down the Qakbot malware, which infected more than 700,000 computers globally, including the UK. The Qakbot malware was a key enabler for facilitating ransomware attacks and was utilised in Conti operations. Today’s designation by the UK and US of further individuals involved in Conti/Trickbot represents the continued efforts to target and disrupt high harm ransomware actors
Media enquiries
Email newsdesk@fcdo.gov.uk
Telephone 020 7008 3100
Contact the FCDO Communication Team via email (monitored 24 hours a day) in the first instance, and we will respond as soon as possible.